
Blogs
- Home
- Blogs

JSON Web Token is a JSON-based open standard ( RFC 7519) means of representing a set of information to be securely transmitted between two parties. A set of information is the set of claims (claim set) represented by the JWT. A claim set consists of zero or more claims represented by the name-value pairs, where the names are strings and the values are arbitrary JSON values. The claims in a JWT are encoded as a JSON object that is used as the payload of a JSON Web Signature (JWS) structure, enabling the claims to be digitally signed. JWTs can be signed using a shared secret (with HMAC algorithm), or a public or private key pair using RSA.
API Gateway can generate a JWT token itself or validate the JWT token generated by a trusted third-party server. API Gateway uses the RSA-based JWT to provide stronger integrity protection to JWTs when API Gateway is the issuer of the token. The JSON-based access tokens contain one or more claims. A claim is any piece of information that serves as an unique identifier, and that the token issuer who generated the token has verified. API Gateway extracts the claims from the JWT, identifies the application and then authorizes access to the protected resource.
In short, JWTs are used as a secure way to authenticate users and share information.
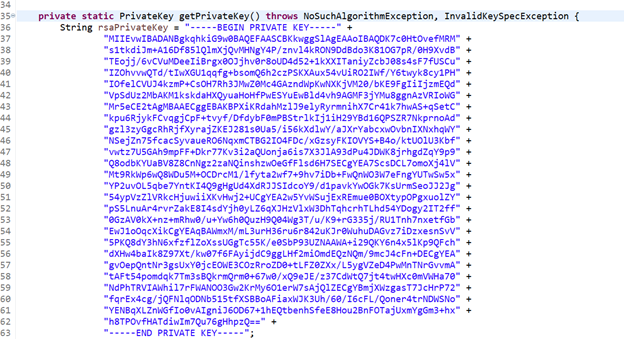
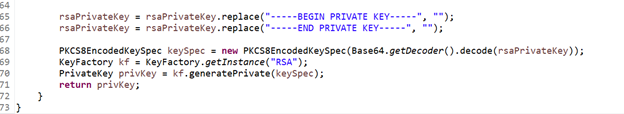
JWTs are typically signed by the issuer using a private key. The receiver of the JWT will verify the signature to ensure the token has not been altered after it was signed by the issuer. For unauthenticated sources, it is difficult to guess the signing key and attempt to alter the claims in the JWT.
However, not all signing algorithms are created equal. Several signing algorithms share a secret value between the issuer and the party verifying the JWT, for example. Others employ public and private keys. Private keys are known only to the issuer, whereas public keys can be shared widely. Signatures can be verified using the public key, but only the private key can be used to create them. This is more secure than a shared secret because the private key only needs to exist in one place.
Because of this, the server does not need to keep a database with the information needed to identify the user. For developers, this is great news — the server that issues the JWT and the server that validates it do not have to be the same.
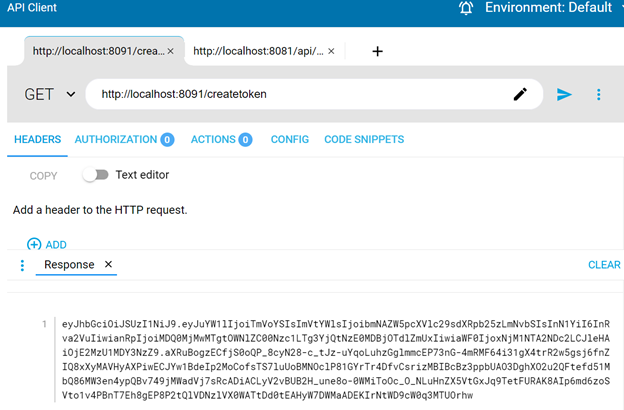
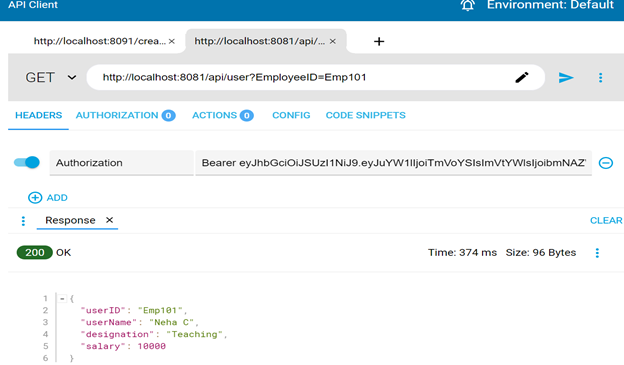
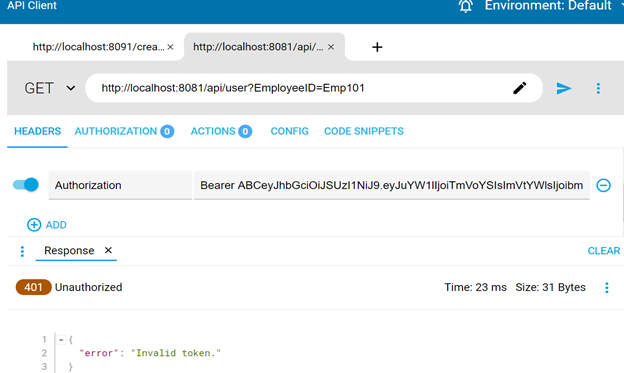
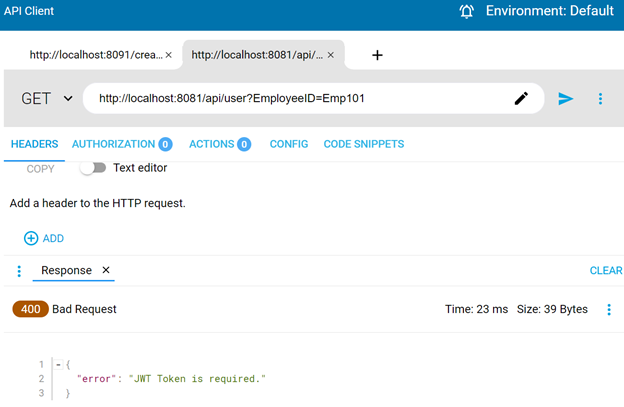
To apply JWT Policy on an API using Text option (i.e. without JWKS) through API Manager. This implies that JWT token is not to be generated by third party. By applying this policy, only authorized clients with valid JWT token can access the API.
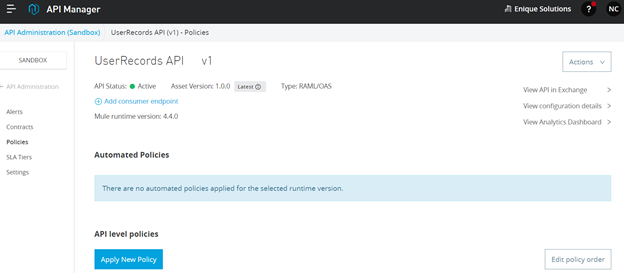
2. Select Policies on the left, and click on “Apply New Policy” button.
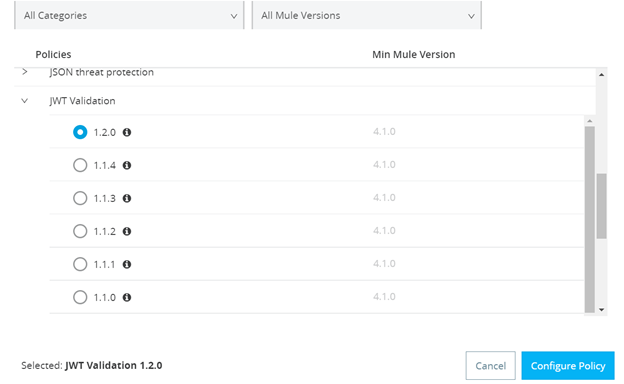
3. In Select Policy window, select the JWT Validation from the list and choose the latest version. Now, click on the “Configure Policy” button.
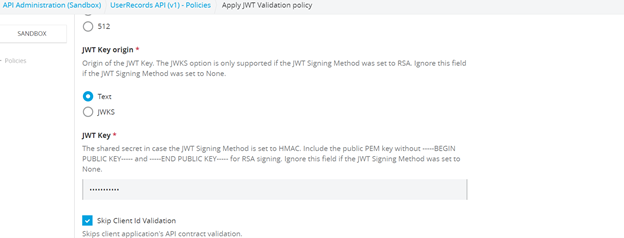
4. In Apply JWT Validation policy, set the following configurations –
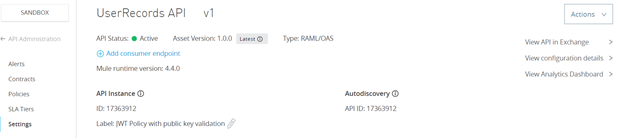
5. Go to Settings in the left pane and add a label to your API “JWT policy with public key validation”
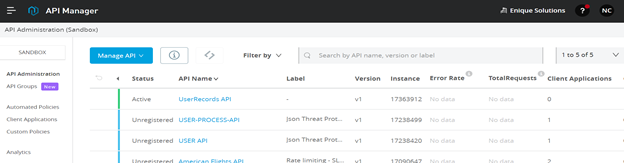
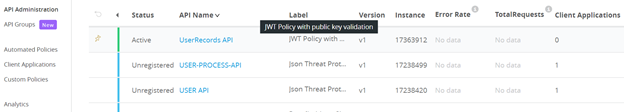
6. Go to API Administration and now you can see your API with added label.

Stateless: JWT’s are self-contained tokens which include authentication information, expiration information, and other user-defined information digitally signed.
Portable: A single token can be used with multiple backends.
Mobile Friendly: Since there are no Cookies Required, it is extremely mobile friendly.
Enhanced Performance: Due to the reduction in network round trip time, it offers better performance
Decoupled/Decentralized: The token can be generated anywhere. Authentication can happen on the resource server, or easily separated into its own server.
To know more about how ENIQUE can help you secure your data journey, reach out to us at info@eniquesolutions.com for a free consultation.